/
Trusted by
Foundational Knowledge
Learn the core concepts of AI agents: what they are, how they work, and features like Retrieval-Augmented Generation (RAG), security, and integrations.
Real-World Applications
Explore how AI agents can automate tasks, support decision-making, and create efficiencies in your work or organization through tailored use-cases.
Hands-On Building
Design and deploy your first AI agent, no coding skills needed. Leave with working AI agents tailored to your own needs. Need help? We'll be there to support.

Secure Agentic AI for LNG Contract Analysis and Compliance
StackAI helps energy companies like Cheniere deploy secure AI agents that automate contract and tender review, extract key terms from complex LNG agreements, streamline regulatory compliance workflows, and connect to internal data sources like SharePoint and Snowflake for faster, more consistent decision-making.
Granular RBAC
Create custom roles and groups
Global Policy
Admins set cross-cutting policy
Agentic Development Life Cycle
The safest path from prototype to production
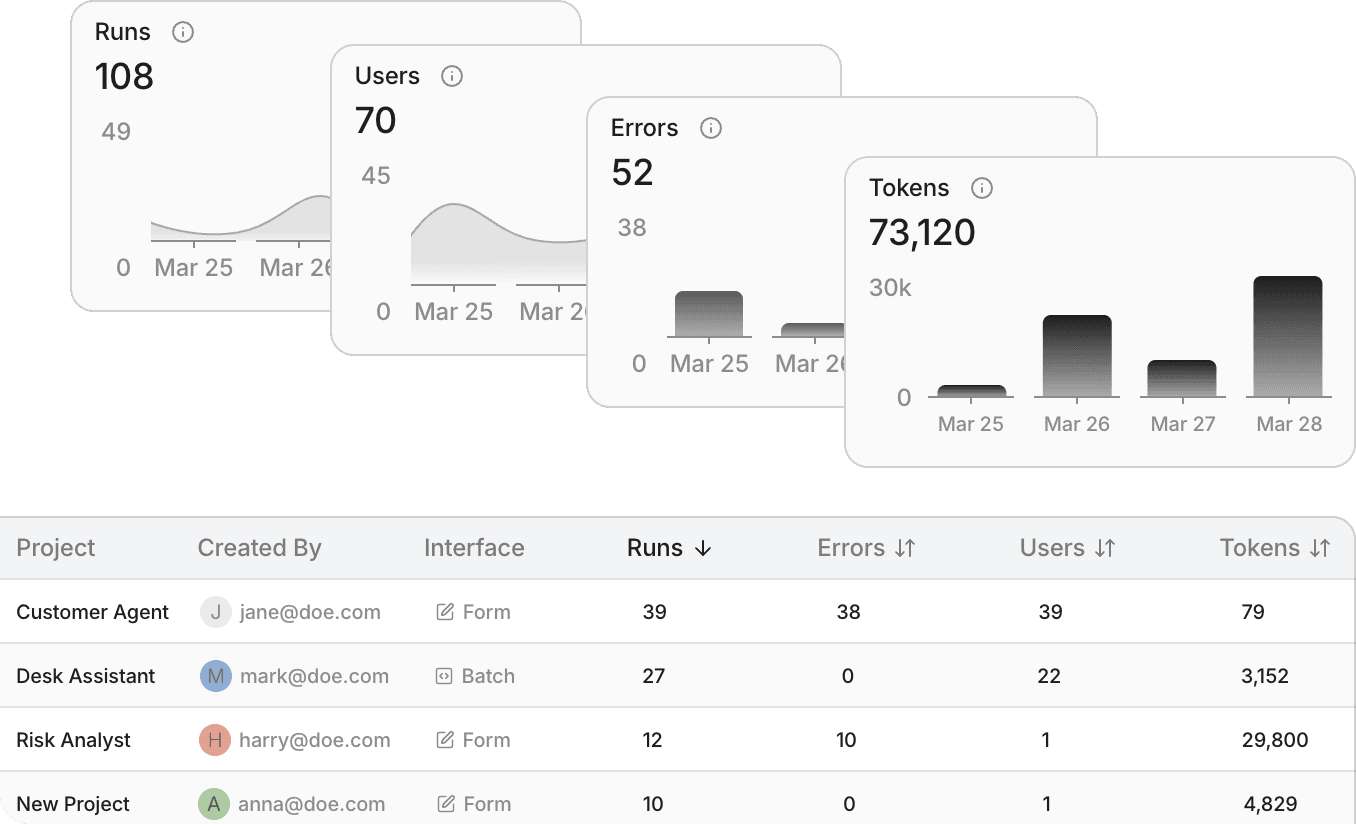
Analytics
Customizable audit logs and global analytics
Delegated Permissions
Enforce end-user access to sensitive information
Scope Control
Assign users and groups to private folders
A leading engineering firm used StackAI to automate resource-intensive operational workflows, cutting staffing cycles by 90% and reducing proposal drafting time by 40%. By deploying AI agents across critical project operations, they dramatically accelerated delivery timelines and freed teams to focus on higher-value work.
Workflows used
Staffing and proposal automation.
90% faster staffing cycles
40% faster proposal drafting

How a Top Engineering Firm Cut Staffing Cycles by 90% and Proposal Drafting Time by 40% with StackAI
integrations
With 100+ enterprise integrations, AI agents built on StackAI can read, write, and execute tasks within your existing systems.

HIPAA
Secure, certified handling of sensitive health information.
Healthcare
001

GDPR
Advanced privacy standards for the protection of personal data.
Europe
002

SOC 2 Type II
Verified security practices for enterprise-grade data protection.
SECURITY
003

ISO 27001
Global excellence in information security management.
global
004



















